I pasted in my certificate, as mentioned in the blog post, I still get the message 'unable to get local issuer certificate'. I verified that git was still working by cloning a GitHub Repository via https. Add Missing Certificate to Squid (Recommended)¶ Web Safety has the ability to add the missing certificates to the Squid intermediate certificate storage. Navigate to UI / Squid / HTTPS / Missing Certificates and upload the PEM file for the certificate as inidicated on the following screenshots. Click Save and Restart to load the storage.
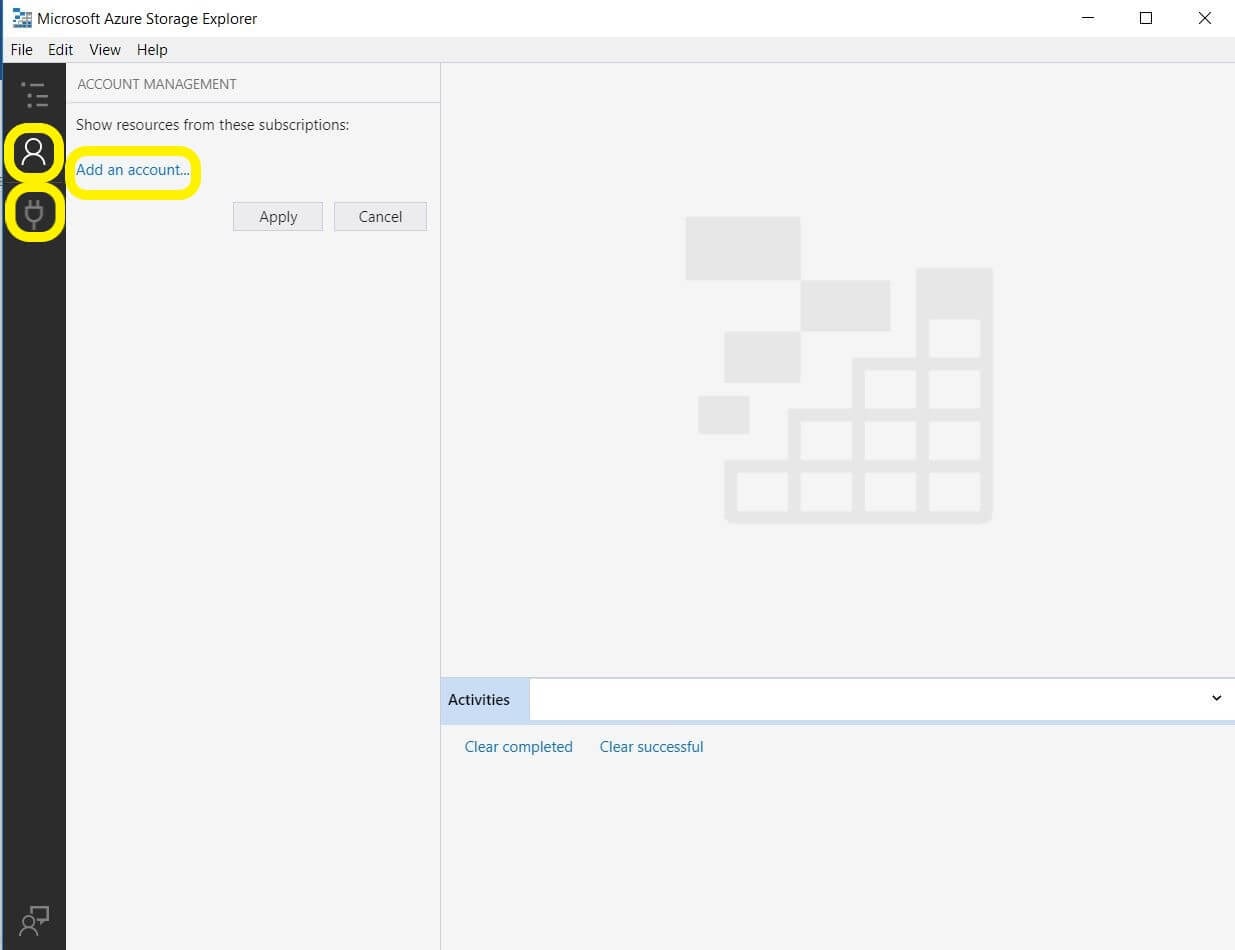
- Azure Storage Explorer Unable To Get Local Issuer Certificate Code
- Azure Storage Explorer Unable_to_get_issuer_cert_locally
When you try to clone a repository, you may have an error like “ ssl certificate problem: unable to get local issuer certificate”And may be the same in command line :
In order to resolve the issue, you will put the Base64 certificat of the TFS Server.

Fixe
- Extract the Base64 Certificat of the TFS server
- Go on the On-premise TFS server with Internet Explorer.
- Click on the lock at the right of the URL bar.
- Click on “View certificates”
- Go on the “Certification Path” tab
- Select the root certificat
- Click on the button “View Certificate”
- Go on the “Details” tab
- Click on the button “Copy to File…”
A wizard window appears:
- click on the “Next >” button
- Select the option “ Base-64 encoded X.509 (.CER)” and then click on “ Next >” button
- Select an extraction location by typing the location with a name for the certificate (example : TFS-ROOT-CERT.CER) or clicking on “Browse” and put the name at the right place
At the end of the Wizard, you will get a summary of your choices, close the window by clicking on “Finish”
Open the file with a text editor like “?otepad++” and Copy the content on the clipboard
- Add the certificate Base-64 content to the ca-bundle.crt
Now, you must open “ Notepad++” with administrator rights
Go on the directory where is install Visual Studio and lookup for the folder “certs”, the path must be the followedC:Program Files (x86)Microsoft Visual Studio2017<Version>Common7IDECommonExtensionsMicrosoftTeamFoundationTeam ExplorerGitmingw32sslcerts
Please find the following array the path for Visual Studio 2017 with each version available.
| Version | Location |
|---|---|
| Enterprise | C:Program Files (x86)Microsoft Visual Studio2017EnterpriseCommon7IDECommonExtensionsMicrosoftTeamFoundationTeam ExplorerGitmingw32sslcerts |
| Professional | C:Program Files (x86)Microsoft Visual Studio2017Professional Common7IDECommonExtensionsMicrosoftTeamFoundationTeam ExplorerGitmingw32sslcerts |
| Community | C:Program Files (x86)Microsoft Visual Studio2017CommunityCommon7IDECommonExtensionsMicrosoftTeamFoundationTeam ExplorerGitmingw32sslcerts |
Open the “ca-bundle.crt” file on “Notepad++” (click right and “ Open with Notepad++”)
Paste the content of the Extracted certificat (Step 1) at the end of the file .crt
Command line
This will solve the issue with Visual Studio 2017, if you want to solve the issue with the command line you must reproduce the pasting on the file “ca-bundle.crt” present on the directory C:Program FilesGitmingw64sslcerts
-->
Azure DevOps Server 2020 | Azure DevOps Server 2019 | TFS 2018 | TFS 2017
This topic explains how to run a v2 self-hosted agent with self-signed certificate.
Work with SSL server certificate
Agent diagnostic log shows:
This error may indicate the server certificate you used on your TFS server is not trusted by the build machine. Make sure you install your self-signed ssl server certificate into the OS certificate store.
You can easily verify whether the certificate has been installed correctly by running few commands.You should be good as long as SSL handshake finished correctly even you get a 401 for the request.
If somehow you can't successfully install certificate into your machine's certificate store due to various reasons, like: you don't have permission or you are on a customized Linux machine.The agent version 2.125.0 or above has the ability to ignore SSL server certificate validation error.
Important
This is not secure and not recommended, we highly suggest you to install the certificate into your machine certificate store.
Pass --sslskipcertvalidation during agent configuration
Note
There is limitation of using this flag on Linux and macOS
The libcurl library on your Linux or macOS machine needs to built with OpenSSL, More Detail
Git get sources fails with SSL certificate problem (Windows agent only)
We ship command-line Git as part of the Windows agent.We use this copy of Git for all Git related operation.When you have a self-signed SSL certificate for your on-premises TFS server, make sure to configure the Git we shipped to allow that self-signed SSL certificate.There are 2 approaches to solve the problem.
Set the following git config in global level by the agent's run as user.
Note
Setting system level Git config is not reliable on Windows. The system .gitconfig file is stored with the copy of Git we packaged, which will get replaced whenever the agent is upgraded to a new version.
Enable git to use SChannel during configure with 2.129.0 or higher version agentPass
--gituseschannelduring agent configurationNote
Git SChannel has more restrict requirement for your self-signed certificate.Self-singed certificate that generated by IIS or PowerShell command may not be capable with SChanel.
Work with SSL client certificate
Azure Storage Explorer Unable To Get Local Issuer Certificate Code
IIS has a SSL setting that requires all incoming requests to TFS must present client certificate in addition to the regular credential.
When that IIS SSL setting enabled, you need to use 2.125.0 or above version agent and follow these extra steps in order to configure the build machine against your TFS server.
Prepare all required certificate information
- CA certificate(s) in
.pemformat (This should contains the public key and signature of the CA certificate, you need put the root ca certificate and all your intermediate ca certificates into one.pemfile) - Client certificate in
.pemformat (This should contains the public key and signature of the Client certificate) - Client certificate private key in
.pemformat (This should contains only the private key of the Client certificate) - Client certificate archive package in
.pfxformat (This should contains the signature, public key and private key of the Client certificate) - Use
SAMEpassword to protect Client certificate private key and Client certificate archive package, since they both have client certificate's private key
- CA certificate(s) in
Install CA certificate(s) into machine certificate store
- Linux: OpenSSL certificate store
- macOS: System or User Keychain
- Windows: Windows certificate store
Pass
--sslcacert,--sslclientcert,--sslclientcertkey.--sslclientcertarchiveand--sslclientcertpasswordduring agent configuration.Your client certificate private key password is securely stored on each platform.
Azure Storage Explorer Unable_to_get_issuer_cert_locally
Learn more about agent client certificate support.

Comments are closed.